NIST CFReDS Hacking Case writeup
NIST Hacking Case
Scenario
On 09/20/04 , a Dell CPi notebook computer, serial # VLQLW, was found abandoned along with a wireless PCMCIA card and an external homemade 802.11b antennae. It is suspected that this computer was used for hacking purposes, although cannot be tied to a hacking suspect, G=r=e=g S=c=h=a=r=d=t. (The equal signs are just to prevent web crawlers from indexing this name; there are no equal signs in the image files.) Schardt also goes by the online nickname of “Mr. Evil” and some of his associates have said that he would park his vehicle within range of Wireless Access Points (like Starbucks and other T-Mobile Hotspots) where he would then intercept internet traffic, attempting to get credit card numbers, usernames & passwords.
Find any hacking software, evidence of their use, and any data that might have been generated. Attempt to tie the computer to the suspect, G=r=e=g S=c=h=a=r=d=t.
A DD image (in seven parts: 1, 2, 3, 4, 5, 6, 7, 8, and notes) and a EnCase image (second part) of the abandoned computer have already been made.
Downloads
# file * 4Dell Latitude CPi.E01: EWF/Expert Witness/EnCase image file format 4Dell Latitude CPi.E02: EWF/Expert Witness/EnCase image file format SCHARDT.001: DOS/MBR boot sector MS-MBR XP english at offset 0x12c "Invalid partition table" at offset 0x144 "Error loading operating system" at offset 0x163 "Missing operating system", disk signature 0xec5dec5d; partition 1 : ID=0x7, active, start-CHS (0x0,1,1), end-CHS (0x24f,254,63), startsector 63, 9510417 sectors SCHARDT.002: data SCHARDT.003: data SCHARDT.004: data SCHARDT.005: data SCHARDT.006: data SCHARDT.007: data SCHARDT.008: data SCHARDT.LOG: ASCII text, with CRLF line terminators
Preparation
$ sudo apt install afflib-tools ewf-tools
# mkdir ewfmnt # ewfmount 4Dell\ Latitude\ CPi.E01 ewfmnt # fdisk -l ewfmnt/ewf1 Disk ewfmnt/ewf1: 4.54 GiB, 4871301120 bytes, 9514260 sectors Units: sectors of 1 * 512 = 512 bytes Sector size (logical/physical): 512 bytes / 512 bytes I/O size (minimum/optimal): 512 bytes / 512 bytes Disklabel type: dos Disk identifier: 0xec5dec5d Device Boot Start End Sectors Size Id Type ewfmnt/ewf1p1 * 63 9510479 9510417 4.5G 7 HPFS/NTFS/exFAT
# mkdir ddmnt # affuse SCHARDT.001 ddmnt # fdisk -l ddmnt/SCHARDT.001.raw Disk ddmnt/SCHARDT.001.raw: 4.54 GiB, 4871301120 bytes, 9514260 sectors Units: sectors of 1 * 512 = 512 bytes Sector size (logical/physical): 512 bytes / 512 bytes I/O size (minimum/optimal): 512 bytes / 512 bytes Disklabel type: dos Disk identifier: 0xec5dec5d Device Boot Start End Sectors Size Id Type ddmnt/SCHARDT.001.raw1 * 63 9510479 9510417 4.5G 7 HPFS/NTFS/exFAT
Questions
1. What is the image hash? Does the acquisition and verification hash match?
# md5sum ewfmnt/ewf1 ddmnt/SCHARDT.001.raw aee4fcd9301c03b3b054623ca261959a ewfmnt/ewf1 aee4fcd9301c03b3b054623ca261959a ddmnt/SCHARDT.001.raw
OK
Answer: aee4fcd9301c03b3b054623ca261959a
$ umount ewfmnt $ umount ddmnt
2. What operating system was used on the computer?
$ mkdir winxp_mnt/ $ sudo mkdir /mnt/ewfmnt $ sudo ewfmount 4Dell_Latitude_CPi.E01 /mnt/ewfmnt/ ewfmount 20140807 $ sudo fdisk -l /mnt/ewfmnt/ewf1 Disk /mnt/ewfmnt/ewf1: 4.54 GiB, 4871301120 bytes, 9514260 sectors Units: sectors of 1 * 512 = 512 bytes Sector size (logical/physical): 512 bytes / 512 bytes I/O size (minimum/optimal): 512 bytes / 512 bytes Disklabel type: dos Disk identifier: 0xec5dec5d Device Boot Start End Sectors Size Id Type /mnt/ewfmnt/ewf1p1 * 63 9510479 9510417 4.5G 7 HPFS/NTFS/exFAT $ sudo mount -o ro,noload,loop,noexec,offset=$((512*63)),show_sys_files,streams_interface=windows /mnt/ewfmnt/ewf1 winxp_mnt/ $ ls winxp_mnt/ $AttrDef AUTOEXEC.BAT hiberfil.sys RECYCLER/ $BadClus boot.ini IO.SYS SETUPLOG.TXT $Bitmap BOOTLOG.PRV MSDOS.--- SUHDLOG.DAT $Boot BOOTLOG.TXT MSDOS.SYS SYSTEM.1ST $Extend/ BOOTSECT.DOS My Documents/ System Volume Information/ $LogFile COMMAND.COM NETLOG.TXT Temp/ $MFTMirr CONFIG.SYS ntdetect.com VIDEOROM.BIN $Secure DETLOG.TXT ntldr WIN98/ $UpCase Documents and Settings/ pagefile.sys WINDOWS/ $Volume FRUNLOG.TXT Program Files/
$ cp ../winxp_mnt/WINDOWS/system32/config/system . $ cp ../winxp_mnt/WINDOWS/system32/config/software . $ cp ../winxp_mnt/WINDOWS/system32/config/SAM .
$ sudo apt install libhivex-bin
Windows OS version( XP ): HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion
$ hivexget software "Microsoft\Windows NT\CurrentVersion" "CurrentBuild"="1.511.1 () (Obsolete data - do not use)" "InstallDate"=dword:41252e3b "ProductName"="Microsoft Windows XP" (snip) "CurrentVersion"="5.1" "CurrentBuildNumber"="2600" "BuildLab"="2600.xpclient.010817-1148" (snip)
Answer: Microsoft Windows XP
3. When was the install date?
From Q2
$ hivexget software "Microsoft\Windows NT\CurrentVersion" "CurrentBuild"="1.511.1 () (Obsolete data - do not use)" "InstallDate"=dword:41252e3b (snip)
https://www.epochconverter.com/hex?q=41252e3b
Answer: GMT: 2004年8月19日 Thursday 22:48:27
4. What is the timezone settings?
$ hivexget system "ControlSet001\Control\TimeZoneInformation" "Bias"=dword:00000168 "StandardName"="Central Standard Time" "StandardBias"=dword:00000000 "StandardStart"=hex(3):00,00,0a,00,05,00,02,00,00,00,00,00,00,00,00,00 "DaylightName"="Central Daylight Time" "DaylightBias"=dword:ffffffc4 "DaylightStart"=hex(3):00,00,04,00,01,00,02,00,00,00,00,00,00,00,00,00 "ActiveTimeBias"=dword:0000012c
Answer: Central Standard Time,Central Daylight Time
5. Who is the registered owner?
From Q2
$ hivexget software "Microsoft\Windows NT\CurrentVersion" (snip) "RegisteredOwner"="Greg Schardt" (snip)
Answer: Greg Schardt
6. What is the computer account name?
$ hivexget system "ControlSet001\Control\ComputerName\ComputerName" "ComputerName"="N-1A9ODN6ZXK4LQ"
Answer: N-1A9ODN6ZXK4LQ
7. What is the primary domain name?
$ hivexget software "Microsoft\Windows NT\CurrentVersion\Winlogon" "AutoRestartShell"=dword:00000001 "DefaultDomainName"="N-1A9ODN6ZXK4LQ" "DefaultUserName"="Mr. Evil" (snip) "AltDefaultUserName"="Mr. Evil" "AltDefaultDomainName"="N-1A9ODN6ZXK4LQ"
Answer: N-1A9ODN6ZXK4LQ
Official Answer?: Evil
8. When was the last recorded computer shutdown date/time?
$ hivexget system "ControlSet001\Control\Windows" (snip) "ShutdownTime"=hex(3):c4,fc,00,07,4d,8c,c4,01
Answer: Fri 27 August 2004 15:46:33 UTC
9. How many accounts are recorded (total number)?
$ hivexsh SAM
Welcome to hivexsh, the hivex interactive shell for examining
Windows Registry binary hive files.
Type: 'help' for help summary
'quit' to quit the shell
SAM\> cd \SAM\Domains\Account\Users\Names
SAM\SAM\Domains\Account\Users\Names> ls
Administrator
Guest
HelpAssistant
Mr. Evil
SUPPORT_388945a0
Answer: 5 accounts
10. What is the account name of the user who mostly uses the computer?
regripperのソースを眺めてシェルスクリプトを作成した。
https://github.com/keydet89/RegRipper3.0/blob/16e0744473ac66ef821f562a23feabb9489a4922/plugins/samparse.pl#L164
https://github.com/keydet89/RegRipper3.0/blob/16e0744473ac66ef821f562a23feabb9489a4922/plugins/samparse.pl#L256
$ cat login-count.sh
sed -ie s/,/' '/g $1
F_array=(`sed -e s/,/' '/g $1`)
printf %d\\n 0x${F_array[67]}${F_array[66]}
rid & user
$ hivexsh SAM (snip) SAM\> cd \SAM\Domains\Account\Users SAM\SAM\Domains\Account\Users> ls 000001F4 #-> to dex 500 -> Admin 000001F5 000003E8 000003EA 000003EB #-> to dex 1003(rid) -> Mr.Evil Names SAM\SAM\Domains\Account\Users> cd Names\Mr. Evil SAM\SAM\Domains\Account\Users\Names\Mr. Evil> lsval "@"=hex(1003):
check F key
sam\SAM\Domains\Account\Users\000003EB> lsval "F"=hex(3):02,00,01,00,00,00,00,00,a0,73,46,b2,47,8c,c4,01,00,00,00,00,00,00,00,00,50,5e,ea,cc,40,86,c4,01,ff,ff,ff,ff,ff,ff,ff,7f,00,00,00,00,00,00,00,00,eb,03,00,00,01,02,00,00,10,02,00,00,00,00,00,00,00,00,0f,00,01,00,00,00,00,00,08,00,c0,f6,06,00 (snip)
check login count
$ cat Mr.Evil 02,00,01,00,00,00,00,00,a0,73,46,b2,47,8c,c4,01,00,00,00,00,00,00,00,00,50,5e,ea,cc,40,86,c4,01,ff,ff,ff,ff,ff,ff,ff,7f,00,00,00,00,00,00,00,00,eb,03,00,00,01,02,00,00,10,02,00,00,00,00,00,00,00,00,0f,00,01,00,00,00,00,00,08,00,c0,f6,06,00 $ bash login-count.sh Mr.Evil 15 $ bash login-count.sh Admin 0 $ bash login-count.sh Guest 0 $ bash login-count.sh HelpAssistant 0 $ bash login-count.sh SUPPORT_388945a0 0
Mr.Evilと同様に他のユーザに対しても試すと他のユーザはログイン回数が0であることが分かった。
Answer:Mr.Evil
11. Who was the last user to logon to the computer?
最後にログインしたユーザは"Software\Microsoft\Windows NT\CurrentVersion\Winlogon"にリストされる。 また、Q.10で全てのユーザのログイン回数を確認したところMr.Evilしかログインが確認できなかった。
$ hivexget software "Microsoft\Windows NT\CurrentVersion\Winlogon" (snip) "DefaultUserName"="Mr. Evil" (snip)
Answer:Mr.Evil
12. A search for the name of “G=r=e=g S=c=h=a=r=d=t” reveals multiple hits. One of these proves that G=r=e=g S=c=h=a=r=d=t is Mr. Evil and is also the administrator of this computer. What file is it? What software program does this file relate to?
$ grep -iR "Greg Schardt" winxp_mnt/ winxp_mnt/Program Files/Look@LAN/irunin.ini:%REGOWNER%=Greg Schardt winxp_mnt/Program Files/Look@LAN/irunin.ini:%USERNAME%=Greg Schardt winxp_mnt/WINDOWS/Look@LAN Setup Log.txt:Value data = Greg Schardt grep: winxp_mnt/$Extend/$ObjId: No such file or directory grep: winxp_mnt/$Extend/$Quota: No such file or directory grep: winxp_mnt/$Extend/$Reparse: No such file or directory grep: winxp_mnt/$Secure: No such file or directory $ cat "winxp_mnt/Program Files/Look@LAN/irunin.ini" | grep "Mr. Evil" %LANUSER%=Mr. Evil %DESKTOP%=C:\Documents and Settings\Mr. Evil\Desktop %STARTMENU%=C:\Documents and Settings\Mr. Evil\Start Menu %STARTMENUPROGRAMS%=C:\Documents and Settings\Mr. Evil\Start Menu\Programs %STARTUP%=C:\Documents and Settings\Mr. Evil\Start Menu\Programs\Startup %MYDOCUMENTSDIR%=C:\Documents and Settings\Mr. Evil\My Documents %SRCFILE%=C:\Documents and Settings\Mr. Evil\Desktop\lalsetup250.exe %SRCDIR%=C:\Documents and Settings\Mr. Evil\Desktop $ cat "winxp_mnt/WINDOWS/Look@LAN Setup Log.txt" | grep "Mr. Evil" C:\Documents and Settings\Mr. Evil\Desktop\Look@LAN.lnk C:\Documents and Settings\Mr. Evil\Desktop\Look@Host.lnk
Answers
What file is it? -> Program\ Files/Look@LAN/irunin.ini
What software program does this file relate to? -> Look@LAN
look@lan
13. List the network cards used by this computer
check: HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkCards
$ hivexsh software (snip) software\> cd Microsoft\Windows NT\CurrentVersion\NetworkCards software\Microsoft\Windows NT\CurrentVersion\NetworkCards> ls 11 2
$ hivexget software "Microsoft\Windows NT\CurrentVersion\NetworkCards\11"
"ServiceName"="{86FC0C96-3FF2-4D59-9ABA-C602F213B5D2}"
"Description"="Compaq WL110 Wireless LAN PC Card"
$ hivexget software "Microsoft\Windows NT\CurrentVersion\NetworkCards\2"
"ServiceName"="{6E4090C2-FAEF-489A-8575-505D21FC1049}"
"Description"="Xircom CardBus Ethernet 100 + Modem 56 (Ethernet Interface)"
Answers
14. This same file reports the IP address and MAC address of the computer. What are they?
分かりづらいが「This same file」は Q.12のことらしい。
$ cat winxp_mnt/Program\ Files/Look@LAN/irunin.ini | egrep "IP|NIC" %LANIP%=192.168.1.111 %LANNIC%=0010a4933e09 (snip)
Answers
- IP addr: 192.168.1.111
- MAC addr: 0010a4933e09
15. An internet search for vendor name/model of NIC cards by MAC address can be used to find out which network interface was used. In the above answer, the first 3 hex characters of the MAC address report the vendor of the card. Which NIC card was used during the installation and set-up for LOOK@LAN?
check 0010a4933e09 -> https://uic.jp/mac/address/0010a4/
Answer: Xircom CardBus Ethernet 100 + Modem 56
16. Find 6 installed programs that may be used for hacking.
check: HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall
$ hivexsh software
(snip)
software\> cd \Microsoft\Windows\CurrentVersion\Uninstall
software\Microsoft\Windows\CurrentVersion\Uninstall> ls
123 Write All Stored Passwords
AddressBook
Anonymizer
Branding
Cain & Abel v2.5 beta45
Connection Manager
CuteFTP
CuteHTML
DirectAnimation
DirectDrawEx
Ethereal
Faber Toys_is1
Fontcore
Forte Agent
ICW
IE40
IE4Data
IE5BAKEX
IEData
Look@LAN_1.0
Microsoft NetShow Player 2.0
mIRC
MobileOptionPack
MPlayer2
NetMeeting
Network Stumbler
OutlookExpress
PCHealth
SchedulingAgent
WinPcapInst
{350C97B0-3D7C-4EE8-BAA9-00BCB3D54227}
{6C31E111-96BB-4ADC-9C81-E6D3EEDDD8D3}
ぶっちゃけどれが悪用されたかはここまででは分からないので、ツールの機能で推測する以上の根拠は無さそうだ。
Answers
- Cain & Abel v2.5 beta45 (password sniffer & cracker)
- Ethereal (packet sniffer)
- 123 Write All Stored Passwords (finds passwords in registry)
- Anonymizer (hides IP tracks when browsing)
- CuteFTP (FTP software)
- Look&LAN_1.0 (network discovery tool)
- NetStumbler (wireless access point discovery tool)
17. What is the SMTP email address for Mr. Evil?
from the list installed programs in Q.16
OutlookExpress Forte Agent
OutlookExpress
++ OutlookExpressのメッセージとアドレス帳の保存場所 ++より
Default: C:\Documents and Settings\[user]\Local Settings\Application Data\Identities\{strings?}\Microsoft\Outlook Express
mailaddress: Not found?
Forte Agent
How do I specify the directory for Agent's database?
There are a couple of ways, depending on your setup. The first and preferred way is via the Start In parameter of the shortcut you use to start Agent. Right-click on the shortcut and select Properties. In the Start In field, enter the path to the directory that contains the agent.ini file. This is how you would set up Agent for multiple servers.
The second way is by using a command line parameter, also in the shortuct. For this method, make sure the Start In field is blank, and add the path to your agent.ini file to the Target field, like this: "\Agent\Agent.exe" "\Agent\Data\agent.ini"
This is handy if you use the same database from multiple locations, like on a laptop with two or more connection types, depending on where you are physically, and it would allow you to specify different connection setups.
AGENT.INI is config file.
$ cat winxp_mnt/Program\ Files/Agent/Data/AGENT.INI | grep -i email EMailAddress="whoknowsme@sbcglobal.net" (snip)
Answer:whoknowsme[@]sbcglobal[.]net
18. What are the NNTP (news server) settings for Mr. Evil?
インストール中にnews serverの設定があるのを見かけたので、config fileにありそうだと考えた。
$ cat "winxp_mnt/Program\ Files/Agent/Data/AGENT.INI" | grep -i newsserver NewsServer="news.dallas.sbcglobal.net"
Answer:news.dallas.sbcglobal.ne
19. What two installed programs show this information?
From Q.17
Answers
- Outlook
- Forte Agent
20. List 5 newsgroups that Mr. Evil has subscribed to?
ここでは全てリストする。
$ ls "Documents and Settings/Mr. Evil/Local Settings/Application Data/Identities/{EF086998-1115-4ECD-9B13-9ADC067B4929}/Microsoft/Outlook Express"
alt.2600.cardz.dbx alt.stupidity.hackers.malicious.dbx
alt.2600.codez.dbx cleanup.log
alt.2600.crackz.dbx 'Deleted Items.dbx'
alt.2600.dbx Folders.dbx
alt.2600.hackerz.dbx free.binaries.hackers.malicious.dbx
alt.2600.moderated.dbx free.binaries.hacking.beginner.dbx
alt.2600.phreakz.dbx free.binaries.hacking.computers.dbx
alt.2600.programz.dbx free.binaries.hacking.talentless.troll-haven.dbx
alt.binaries.hacking.beginner.dbx free.binaries.hacking.talentless.troll_haven.dbx
alt.binaries.hacking.computers.dbx free.binaries.hacking.utilities.dbx
alt.binaries.hacking.utilities.dbx free.binaries.hacking.websites.dbx
alt.binaries.hacking.websites.dbx Inbox.dbx
alt.dss.hack.dbx Offline.dbx
alt.hacking.dbx Outbox.dbx
alt.nl.binaries.hack.dbx
Answers
alt.2600.cardz, alt.2600.codez, alt.2600.crackz, alt.2600, alt.2600.hackerz, alt.2600.moderated, alt.2600.phreakz, alt.2600.programz, alt.binaries.hacking.beginner, alt.binaries.hacking.computers, alt.binaries.hacking.utilities, alt.binaries.hacking.websites, alt.dss.hack, alt.hacking, alt.nl.binaries.hack, alt.stupidity.hackers.malicious, free.binaries.hackers.malicious, free.binaries.hacking.beginner, free.binaries.hacking.computers, free.binaries.hacking.talentless.troll-haven, free.binaries.hacking.talentless.troll_haven, free.binaries.hacking.utilities
21. A popular IRC (Internet Relay Chat) program called MIRC was installed. What are the user settings that was shown when the user was online and in a chat channel?
問いが曖昧である。
Answers
$ cat "Program Files/mIRC/mirc.ini" (snip) [mirc] user=Mini Me email=none@of.ya nick=Mr anick=mrevilrulez host=Undernet: US, CA, LosAngelesSERVER:losangeles.ca.us.undernet.org:6660GROUP:Undernet (snip)
22. This IRC program has the capability to log chat sessions. List 3 IRC channels that the user of this computer accessed.
$ ls "Program Files/mIRC/logs" '#Chataholics.UnderNet.log' '#evilfork.EFnet.log' '#ISO-WAREZ.EFnet.log' '#mp3xserv.UnderNet.log' '#CyberCafe.UnderNet.log' '#funny.UnderNet.log' '#LuxShell.UnderNet.log' '#thedarktower.AfterNET.log' '#Elite.Hackers.UnderNet.log' '#houston.UnderNet.log' m5tar.UnderNet.log '#ushells.UnderNet.log'
Answers
#Chataholics.UnderNet, #CyberCafe.UnderNet.log, #Elite.Hackers.UnderNet #evilfork.EFnet, #funny.UnderNet, #houston.UnderNet, #ISO-WAREZ.EFnet, #LuxShell.UnderNet, m5tar.UnderNet, #mp3xserv.UnderNet.log, #thedarktower.AfterNET, #ushells.UnderNet
23. Ethereal, a popular “sniffing” program that can be used to intercept wired and wireless internet packets was also found to be installed. When TCP packets are collected and re-assembled, the default save directory is that users \My Documents directory. What is the name of the file that contains the intercepted data?
$ ls Documents\ and\ Settings/Mr.\ Evil/ 'Application Data' Favorites 'My Documents' ntuser.dat.LOG Recent Templates Cookies interception NetHood ntuser.ini SendTo Desktop 'Local Settings' NTUSER.DAT PrintHood 'Start Menu' $ file Documents\ and\ Settings/Mr.\ Evil/interception Documents and Settings/Mr. Evil/interception: pcap capture file, microsecond ts (little-endian) - version 2.4 (Ethernet, capture length 65535)
Answer: Documents\ and\ Settings/Mr.\ Evil/interception
24. Viewing the file in a text format reveals much information about who and what was intercepted. What type of wireless computer was the victim (person who had his internet surfing recorded) using?
$ tshark -q -r interception -z conv,ip
================================================================================
IPv4 Conversations
Filter:<No Filter>
| <- | | -> | | Total | Relative | Duration |
| Frames Bytes | | Frames Bytes | | Frames Bytes | Start | |
192.168.254.2 <-> 207.68.174.248 117 68178 145 29226 262 97404 0.000000000 231.6677
192.168.254.254 <-> 239.255.255.250 0 0 80 27728 80 27728 8.157222000 203.6836
65.54.179.195 <-> 192.168.254.2 37 5756 23 22523 60 28279 220.589546000 6.4585
65.54.179.230 <-> 192.168.254.2 25 4282 17 3586 42 7868 81.737500000 148.4987
65.54.183.198 <-> 192.168.254.2 7 1406 4 2881 11 4287 220.082099000 0.3187
192.168.254.3 <-> 192.168.254.255 0 0 1 258 1 258 216.396178000 0.0000
================================================================================
the victim: 192.168.254.2
Wireshark によるパケット解析講座 3: ホストとユーザーを特定するより
どれかを見つければ良い。今回はhttpがあったので。
$ tshark -r interception -z follow,http,ascii,1 -q
===================================================================
Follow: http,ascii
Filter: tcp.stream eq 1
Node 0: 192.168.254.2:1338
Node 1: 207.68.174.248:80
883
GET /content/images/img_ppc_sharkfin_MSNLogo.gif HTTP/1.1
Accept: */*
UA-OS: Windows CE (Pocket PC) - Version 4.20
UA-color: color16
UA-pixels: 240x320
UA-CPU: Intel(R) PXA255
UA-Voice: FALSE
Referer: http://mobile.msn.com/hm/folder.aspx?ts=1093601294&fts=1093566459&folder=ACTIVE&msg=0
UA-Language: JavaScript
Accept-Encoding: gzip, deflate
If-Modified-Since: Wed, 19 May 2004 18:47:04 GMT
If-None-Match: "4098f2add13dc41:8e4"
User-Agent: Mozilla/4.0 (compatible; MSIE 4.01; Windows CE; PPC; 240x320)
Host: mobile.msn.com
Connection: Keep-Alive
Cookie: lc=en-US; cr=1; MSPAuth=5vuMneQNFDh0sFVrAbKrt*q6edOGfSSmKzi3lT1CIh6FdbNqQyPyqubrB97DYRuoTwoA5kp1iTd3eTZ3TUiZ45LQ$$; MSPProf=5ynNj8z2mEi3KQzUnhBOK5dmrXWUam5W2H3bXqJgZE5uFZ7OFVIdTd8rwZLZfLhhQB8q*Sto5O8d!UJp8ulXjB5g4RJME!*WBUVqwsUvAh8UuflyJMTMQt*6C4vjOyvqgDT5F!XAMjAg0!vkXYwzhbCkVlAO1b2zXMjlXnmPnOpETgsIPX0coWMQ$$
218
HTTP/1.1 304 Not Modified
Server: Microsoft-IIS/5.0
Date: Fri, 27 Aug 2004 15:36:35 GMT
X-Powered-By: ASP.NET
P3P:CP="BUS CUR CONo FIN IVDo ONL OUR PHY SAMo TELo"
ETag: "4098f2add13dc41:8e5"
Content-Length: 0
===================================================================
Answer: Windows CE (Pocket PC) - Version 4.20
25. What websites was the victim accessing?
$ tshark -r interception -Y "ip.src==192.168.254.2" -Tfields -e http.host | sort -u login.passport.com login.passport.net mobile.msn.com www.passportimages.com
Answers
- login.passport.com
- login.passport.net
- mobile.msn.com
- www.passportimages.com
26. Search for the main users web based email address. What is it?
$ find . -name "index.dat" ./Documents and Settings/Default User/Cookies/index.dat ./Documents and Settings/Default User/Local Settings/History/History.IE5/index.dat ./Documents and Settings/Default User/Local Settings/Temporary Internet Files/Content.IE5/index.dat ./Documents and Settings/LocalService/Cookies/index.dat ./Documents and Settings/LocalService/Local Settings/History/History.IE5/index.dat ./Documents and Settings/LocalService/Local Settings/Temporary Internet Files/Content.IE5/index.dat ./Documents and Settings/Mr. Evil/Cookies/index.dat ./Documents and Settings/Mr. Evil/Local Settings/History/History.IE5/index.dat ./Documents and Settings/Mr. Evil/Local Settings/History/History.IE5/MSHist012004081620040823/index.dat ./Documents and Settings/Mr. Evil/Local Settings/History/History.IE5/MSHist012004082520040826/index.dat ./Documents and Settings/Mr. Evil/Local Settings/History/History.IE5/MSHist012004082620040827/index.dat ./Documents and Settings/Mr. Evil/Local Settings/History/History.IE5/MSHist012004082720040828/index.dat ./Documents and Settings/Mr. Evil/Local Settings/Temporary Internet Files/Content.IE5/index.dat ./WINDOWS/PCHEALTH/HELPCTR/OfflineCache/index.dat ./WINDOWS/system32/config/systemprofile/Cookies/index.dat ./WINDOWS/system32/config/systemprofile/Local Settings/History/History.IE5/index.dat ./WINDOWS/system32/config/systemprofile/Local Settings/History/History.IE5/MSHist012004081920040820/index.dat ./WINDOWS/system32/config/systemprofile/Local Settings/Temporary Internet Files/Content.IE5/index.dat
linuxだと良さそうなindex.dat用のツールが見つからなかったのでwindows環境のツールを使用
IE HistoryView: Freeware Internet Explorer History Viewer
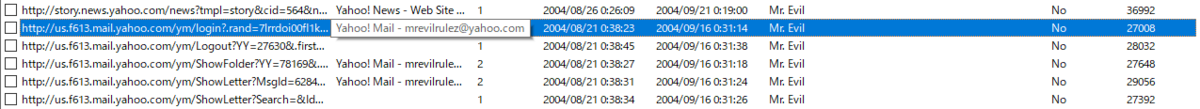
http://us.f613.mail.yahoo.com/ym/login?.rand=7lrrdoi00fl1k&.first=1 Yahoo! Mail - mrevilrulez@yahoo.com
Answer:mrevilrulez@yahoo.com
ページタイトルでメールアドレス取得か...。
27. Yahoo mail, a popular web based email service, saves copies of the email under what file name?
ページを読み込んだときのキャッシュを探すということ?
$ strings "Documents and Settings/Mr. Evil/Local Settings/Temporary Internet Files/Content.IE5/index.dat" (snip) URL http://us.f613.mail.yahoo.com/ym/ShowLetter?MsgId=6284_1110_22_443_55_0_1_-1_0&Idx=0&YY=60138&.first=1&inc=25&order=down&sort=date&pos=0&view=&head=&box=Inbox ShowLetter[1] HTTP/1.1 200 OK P3P: policyref="http://p3p.yahoo.com/w3c/p3p.xml", CP="CAO DSP COR CUR ADM DEV TAI PSA PSD IVAi IVDi CONi TELo OTPi OUR DELi SAMi OTRi UNRi PUBi IND PHY ONL UNI PUR FIN COM NAV INT DEM CNT STA POL HEA PRE GOV" Transfer-Encoding: chunked Content-Type: text/html Content-Encoding: gzip ~U:mr. evil URL http://us.f613.mail.yahoo.com/ym/ShowLetter?MsgId=6284_1110_22_443_55_0_1_-1_0&Idx=0&YY=60138&.htm ShowLetter[1].htm HTTP/1.0 200 OK Content-Length: 42277 Content-Type: text/html (snip)
ここら辺が怪しいか。
$ find . -name "ShowLetter*"
./Documents and Settings/Mr. Evil/Local Settings/Temporary Internet Files/Content.IE5/HYU1BON0/ShowLetter[1]
./Documents and Settings/Mr. Evil/Local Settings/Temporary Internet Files/Content.IE5/HYU1BON0/ShowLetter[1].htm
./Documents and Settings/Mr. Evil/Local Settings/Temporary Internet Files/Content.IE5/PN0J7OQM/ShowLetter[1].htm
$ cat "./Documents and Settings/Mr. Evil/Local Settings/Temporary Internet Files/Content.IE5/HYU1BON0/ShowLetter[1].htm" |html2text
(snip)
bank_of_america/020204_checkbook.gif] Welcome to Yahoo! Mail.
Free_Checking_w/
Direct_Deposit Dear mrevilrulez@yahoo.com, [http://
[http://us.a1.yimg.com/us.yimg.com/a/ra/ us.i1.yimg.com/
ratemymortgage/ Welcome to Yahoo! Mail, a smarter way of keeping in touch. With a whopping 100MB of email storage, message us.yimg.com/i/us/
282153_021004ratemymortgage21_25x25.gif] size up to 10MB, and great virus and spam protection, it's hard to believe it's free! Start using your new pim/pr/trap/
Get_2.9%*_at address right away: mrevilrulez@yahoo.com template1_girl.jpg]
RateMyMortgage
[http://us.a1.yimg.com/us.yimg.com/a/re/ Tell the world. QUICK WAYS
realtytrac/25x25_0709804.gif] You have a new Yahoo! Mail address, so spread the word to family and friends. Send_an_email_now. TO GET STARTED:
1/2_price_homes
Click_here_now. Set up your Address Book. Announce your new
Now's the time to organize your contacts in one place. Enter_addresses_now and make it easy to get in touch. Yahoo! Mail
address. Compose
Get smart about spam. a_message.
Our Anti-Spam_Resource_Center can help you keep spam from reaching your inbox. Learn how to use filters
effectively, block mail from specific addresses and domains, and much more. Make Yahoo! Mail
your everyday
Personalize your email experience. email. Set_as
Create_your_own_signature, and choose_colors_and_fonts for your messages. default for easy
access.
Need even more? You got it.
When you're ready for more, move up to Yahoo! Mail Plus. It provides virus cleaning powered by Norton Put your contacts
AntiVirus*, more powerful spam protection, a virtually unlimited 2GB of email storage, no graphical ads, and within easy
much more. Learn_more. reach. Set_up
your_Address
Have fun using your Yahoo! Mail account! Book.
Sincerely,
[http:// The Yahoo! Mail Team [http://
us.i1.yimg.com/ us.i1.yimg.com/
us.yimg.com/i/ us.yimg.com/i/
us/pim/pr/trap/ us/pim/pr/trap/
em2_cr3.gif] em2_cr4.gif]
*Not all viruses can be detected and cleaned. Please be aware that there is a risk involved whenever downloading
email attachments to your computer or sending email attachments to others and that, as provided in the Terms of
Service, neither Yahoo! nor its licensors are responsible for any damages caused by your decision to do so.
Please do not reply to this message. This is a service email related to your use of Yahoo! Mail. To learn more about
Yahoo!'s use of personal information, including the use ofweb_beaconsin HTML-based email, please read our Privacy
Policy. Yahoo! Mail is located at 701 First Avenue, Sunnyvale, CA 94089.
Copyright © 2004 Yahoo! Inc. All rights reserved. Terms_of_Service
The HTML graphics in this message have been displayed. [Edit_Preferences - What's_This?]
(snip)
Answer: ShowLetter[1].htm
28. How many executable files are in the recycle bin?
$ ls RECYCLER/S-1-5-21-2000478354-688789844-1708537768-1003/ Dc1.exe Dc2.exe Dc3.exe Dc4.exe desktop.ini INFO2
Answer:4
29. Are these files really deleted?
Answer:ごみ箱に移動しただけで削除されていない
30. How many files are actually reported to be deleted by the file system?
$ strings RECYCLER/S-1-5-21-2000478354-688789844-1708537768-1003/INFO2 C:\Documents and Settings\Mr. Evil\Desktop\lalsetup250.exe C:\Documents and Settings\Mr. Evil\Desktop\netstumblerinstaller_0_4_0.exe C:\Documents and Settings\Mr. Evil\Desktop\WinPcap_3_01_a.exe C:\Documents and Settings\Mr. Evil\Desktop\ethereal-setup-0.10.6.exe
Answer:4
しかし......
INFO2には4つのファイルがリストされている。
Autopsyはfilesystemから365のDeletedFileを発見した。
official answer is 3???????????
Help me...........
check MFT?
31. Perform a Anti-Virus check. Are there any viruses on the computer?
install clamAV
$ sudo clamscan -ir --quiet --log=../scan.log . (snip) $ cat scan.log (snip) ----------- SCAN SUMMARY ----------- Known viruses: 8580277 Engine version: 0.103.3 Scanned directories: 767 Scanned files: 11311 Infected files: 22 Data scanned: 1864.52 MB Data read: 1794.54 MB (ratio 1.04:1) Time: 2406.458 sec (40 m 6 s) Start Date: 2021:11:28 06:04:29 End Date: 2021:11:28 06:44:36
Answer: Known viruses: 8580277
WOW